
Why Choose Us
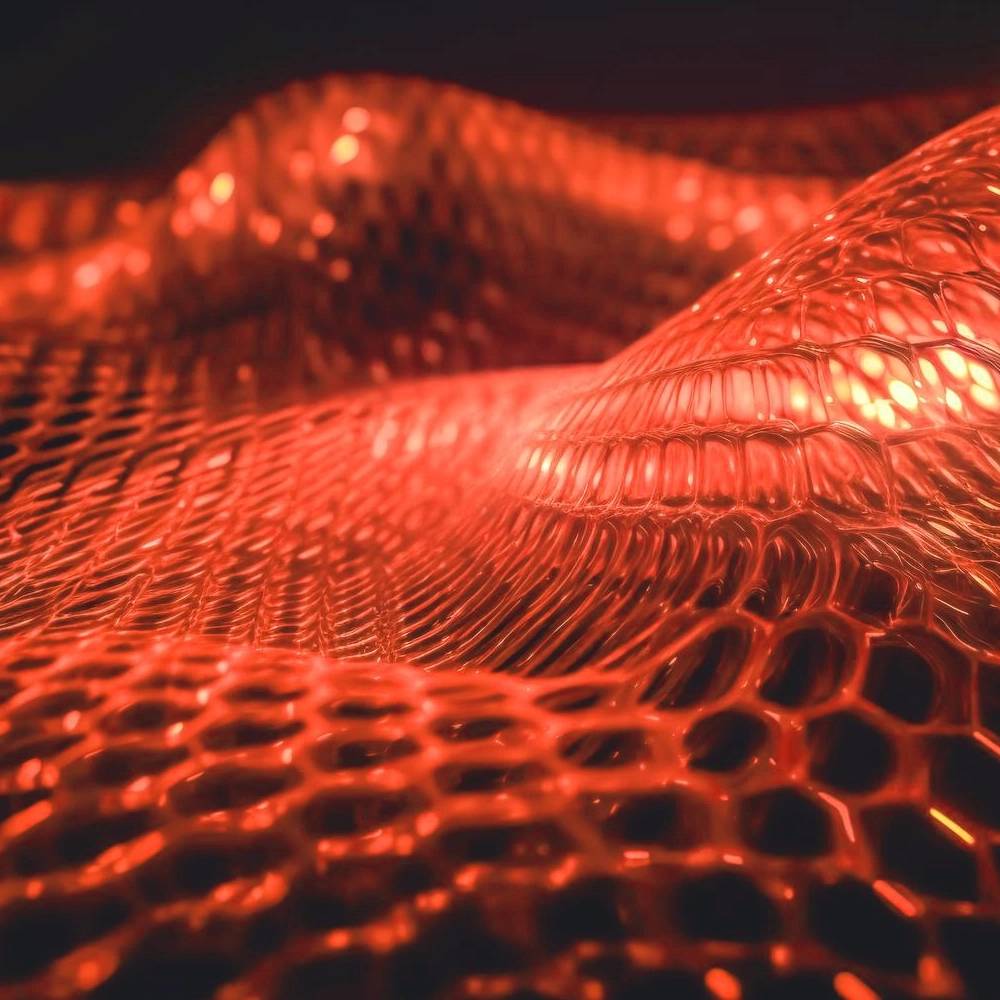
Complete Cyber Defense Against Modern Attacks
Stay protected with a fully integrated defense strategy built for today’s complex cyber landscape. From ransomware to phishing and zero-day exploits, we provide comprehensive protection across networks, endpoints, and cloud environments.
Start with a Free Cyber Risk Baseline.